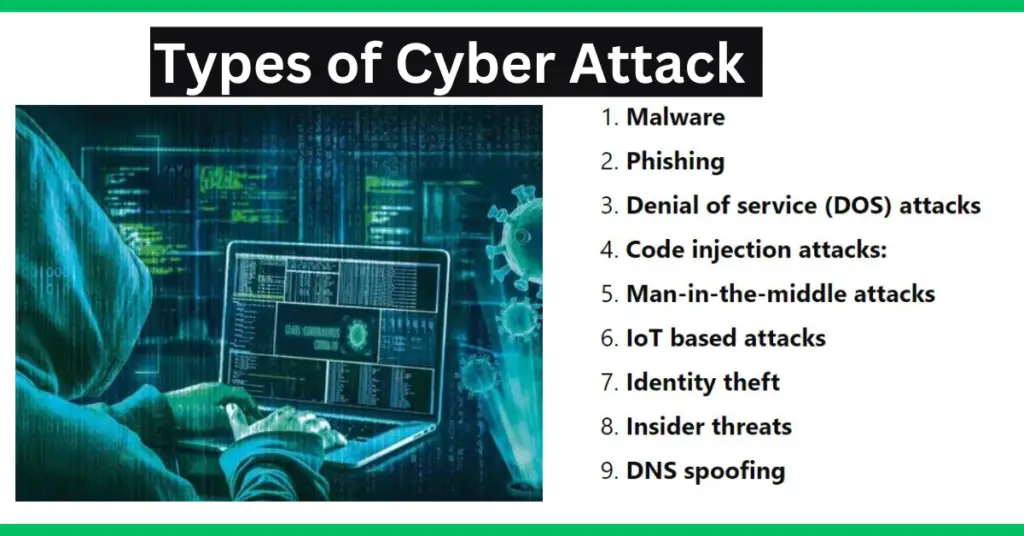
This article describes types of cyber attacks like malware, phishing, DOS, code injection, IoT-based threats, identity theft, insider threats, DNS spoofing, etc.
In industrial automation, networking is a very important tool because it helps in proper communication. It is essential that industrial networking remains intact in any plant. Data sharing is today’s demand in almost every industry. So, it is important that data too remains secured.
Cybersecurity is a major issue in industrial automation. Data gets hacked and the whole network system can get damaged. Any leakage of data is always a threat to any industry. So, it is necessary to see what types of cyber-attacks can be done in an industry. In this post, we will discuss the types of cyber-attacks.
What is a cyber-attack?
Simply, suppose you have a computer system. The system is connected to the internet. In industrial automation, apart from the internet, a PC system is networked to other PCs too. This is done for data sharing. So, for example, if we take an electrical grid automation system, networking is a very integral part of the process. Electrical data is continuously shared inside the plant and even on cloud networking. Now, suppose this PC system gets some unauthorized access from a source through the network and gains control of the system. Such a type of issue is called a cyber-attack.
Cyber-attack is a type of problem that occurs in PC systems, through networking or other types of data-sharing elements and provides illegal access to some hackers or miscreants. Due to this, they can get all data and even control the system without permission. This poses a serious threat to the overall plant system, as your data is being shared with other sources now.
Types of cyber-attacks:
There are the following types of cyber attacks.
- Malware
- Phishing
- Denial of service (DOS) attacks
- Code injection attacks:
- Man-in-the-middle attacks
- IoT based attacks
- Identity theft
- Insider threats
- DNS spoofing
Now, we will discuss each type of cyber attack in detail.

1. Malware
Malware is a software code or program, which is created by hackers and installed illegally in the PC system. This code can do any type of damage, like locking an application and asking for payment in return, collecting information from web history, showing illegal ads to the user by tracking his activity, creating copies of files in the computer and causing phishing, illegal file deletion or modification, etc.
Malware is a type of cyber attack that comprises subsets like ransomware, trojans, spyware, viruses, worms, keyloggers, bots, cryptojacking.
2. Types of Cyber Attacks- Phishing:
In this attack, you will get spam emails and notifications on your PC. It will look very genuine to a real email or notification, and force the user to do some activity. This activity information will be gathered immediately by the hacker and he can then use it to gain access to some secure accounts. It is basically a fake way to make the user believe that it is a real one. Thinking about this, the user can unknowingly share passwords, account information, and other sensitive information.
3. Denial of service (DOS) attacks:
As the name defines, software applications or even the whole PC sometimes is denied access to the users. The user will either not use the system then, or he will be asked to pay an amount in return. The networking system, thus gets impacted in a major way and your work gets halted frequently. This type of cyber attack automatically reduces production, efficiency, and reliability.
4. Code injection attacks:
Code injection means an illegal software code is installed in the system by the hacker. These codes can be anything like injecting malicious software statements and gathering information from the database, injecting malicious scripts in the webpage when opened, and gathering information from surfing activity, etc.
5. Man-in-the-middle attacks:
When a user is communicating or interacting with some other user on the internet or other type of sharing network, a hacker can act as a middle person by listening or reading the interaction. Basically, it is a type of spy attack in which a third-party user is illegally listening to information shared between two users. The hacker can also use it to send messages his way, making both users believe that the message is being sent between both of them. But, in reality, the third person is sending and receiving messages.
6. IoT-based attacks:
IoT is extensively used in industrial automation nowadays, and because IoT is purely based on networking, the technology is being used illegally by hackers to gain access to sensitive industrial information and control it. Also, with the advent of 5G networks in IoT, hacking is made easier in this type of attack.
7. Types of Cyber Attacks- Identity theft:
As the name implies, a hacker steals user information from a user and acts as his identity for other persons on the network system. Due to this, they believe that the real person is here and they unknowingly share data or other sensitive information with him. This theft is a major crime and one of the most trending one cyber-attacks.
8. Insider threats:
This is one such type in which a company never believes in and takes the least precautions. Basically, some office staff get access to the systems and when they get it for good company use, they in turn use it for their benefit. Providing privileges to employees without knowing their real background or work, can hamper the activities in a great way. Because they know the network systems properly, they also know how to be safe in this and perform their illegal activities without informing anyone. This cyber-attack basically arises from unwanted trust in some employees and providing them with not required access.
9. DNS spoofing:
DNS (domain name system) spoofing allows the users to work on a duplicate DNS website or server. This is because it looks very genuine to the real one and hardly produces any doubt in the minds of users. Once the user reaches this website, all the information activities done by him will be immediately tracked by hackers. This issue occurs to poor DNS server architecture and weak network coding.
In this way, we saw some most general types of cyber-attacks in industrial automation.